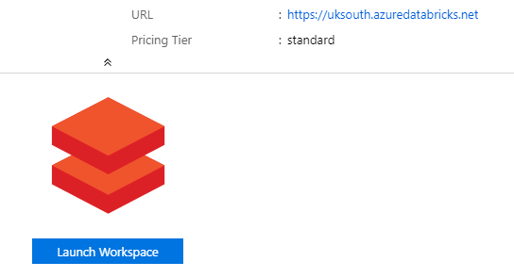
In Part 3 of this blog series we briefly mentioned the two methods to access the Azure Databricks web interface, either through the "Launch Workspace" icon in the portal or via a URL. But now let's think about other users.
Azure Databricks Authentication
Authentication to the web-based interface is performed using our Azure AD account and happens automatically when accessed.
Access
But what about for new user, how do we grant them access?
When we navigated to the Azure Databricks resource within the portal we found that we could use "Launch Workspace" to access our workspace as we have an account with sufficient privileges.
If we share this "Launch Workspace" link with a low privileged user it will throw the following error.
Your account user@domain.onmicrosoft.com does not have Owner or Contributor role on the Databricks workspace resource in the Azure Portal, which is required to "Launch Workspace". If your admin has already added you to this workspace, click "Sign in" above. Otherwise, please ask your administrator to grant you access or add you as a user directly in the Databricks workspace.
Now we could grant Owner or Contributor role for high privilege users and let them use this method, but what we actually want to do is use the URL.
We can get the URL from the same page and pass this directly to our users. For example in the image above this is https://uksouth.azuredatabricks.net, but before we send them the link we need to sort out their access or they will get this error:
The workspace you are trying to access does not exist in this Azure region, or your account user@domain.onmicrosoft.com does not belong to any Databricks workspace in the region. Please ask your administrator to add you as a user, or click here to logout of Azure Active Directory and login with a different user.
This error is pretty obvious we need to add them as a user.
Granting a user access
In order to allow another user access to Azure Databricks we could either grant them Owner or Contributor role on the Azure Databricks workspace resource or add the user explicitly within the Admin Console. Adding users in the Admin Console rather than with Owner or Contributor role will assign less permissions and should be the preferred option.
The Admin Console can be accessed within Azure Databricks by selecting the actor icon and picking the relevant menu option. The user can then be added using the "Add User" button. Internal groups can be created and users assigned to provide granular security to folders and workspaces.
Be aware that at the time of writing this article in August 2019 that the ability to add external user groups in Azure Databricks is not available e.g. an Azure AD group cannot be added to provision users, but each user must be added individually.


